The Dangers of the Remote Desktop Protocol: Tips for Safeguarding

The Remote Desktop Protocol (RDP) is undoubtedly an invaluable tool for the modern IT infrastructure. It allows users to connect to and control remote computers over the network. This function is particularly popular in companies for IT administration, whether for support or remote maintenance of systems.
How Cyber Risk Assessments Optimize SMB IT Security
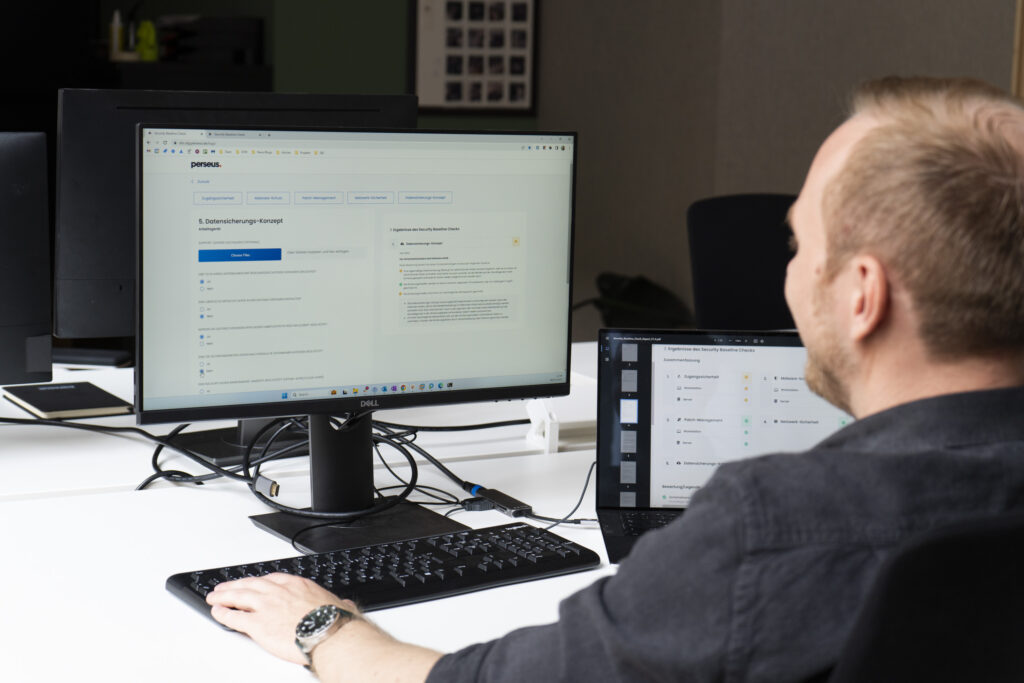
For several years now, cyber attacks have been one of the biggest business risks for German companies. Above all, the negative effects, such as data loss or long-lasting business interruptions, are causing problems for the companies. For some, a cyber attack can even threaten their existence. Reducing one’s own cyber risk and thus avoiding cyber attacks should be at the top of the priority list for companies, especially small and medium-sized enterprises.
In focus: IT security incident across three corners

A restaurant was informed about an IT security incident at a software provider used whose platform is used for ordering, administration and payments. Attackers gained unauthorized access to personal customer data, including names, email addresses and, in some cases, credit card details. The trigger was the misconduct of an external accounting employee who accidentally entered her access data on a fake login page that looked deceptively similar to the original platform.
In Focus: Quadruple Email Scam Scam

Cybercriminals rely on email scams. But anyone who thinks that criminals only send clumsy phishing attempts with poorly written, faulty emails is mistaken. Criminals sometimes put a lot of effort into planning, designing, and executing email fraud. The experts of the Incident Response Management Team have recorded an increase in these attacks. To show you how sophisticated some of these attacks are, we present the following case. You will see the attackers send fake emails, misuse the names of well-known companies for their scam, invent products, create fake websites, copy real companies, and more.
Unveiling the Dark Web: Phishing as a Service (PhaaS)

In the depths of the dark web, a market is thriving where illegal services are offered to those willing to pay a price. Among the services, phishing as a service (PhaaS) proves to be a particularly popular machine that offers access to cybercriminal craft to anyone who has a score to settle or wants to enrich themselves in an illegal way.
Critical vulnerability in Microsoft Exchange Server
20.2.2024 Critical vulnerability in Microsoft Exchange Server Microsoft’s latest update shows that, by exploiting a vulnerability (CVE-2024-21410), attackers are able to carry out a so-called NTLM relay attack, also known as “Pass the Hash”. NTLM is a set of security protocols that authenticate the identity of users and the confidentiality of their activities. Threat actors […]
Easy game for cybercriminals? The shortage of skilled workers in IT security

In today’s digital age, where nearly every aspect of our lives is interconnected and dependent on technology, cybersecurity plays a crucial role. To protect yourself from cyber threats, trained IT security experts are essential in companies.
Business email compromise / compromise of business emails
Business email compromise / compromise of business emails Compromise of business email traffic (business email compromise or BEC for short) is when email traffic is infiltrated, compromised or manipulated. BEC also includes when someone impersonates a person in the company to get the recipient to share confidential information, make financial transactions or perform other actions […]
Patches
Patches What are patches? The word “patch” comes from the English and means “mending”. This describes what it means and its functionality very well: just as a patch can plug a hole, patches close gaps in IT applications. Software applications are updated, improved, extended or even corrected with patches. Under certain circumstances, this can happen […]
Quishing
Quishing What is quishing? The word “quishing” is a combination of the term “phishing” and the abbreviation “QR” and describes phishing attacks via a QR code. Excursus: What is a QR code? QR stands for “Quick Response”. It is a two-dimensional code that displays information in a highly abbreviated form and can be called up […]

