NIS 2 EU Directive: “Hardly manageable?” – With Perseus, yes!

Cyberattacks and the associated consequences such as business interruptions have been among the greatest risks for companies for years – worldwide.
A separation doesn’t always have to hurt!

“Never change a winning team”. That’s the saying. That this attitude is not always advantageous is shown by cyber incidents that occur due to outdated technologies and unpatched applications. Surveys now show that the modernization of IT infrastructures in particular is at the top of the priority list of IT expert teams.
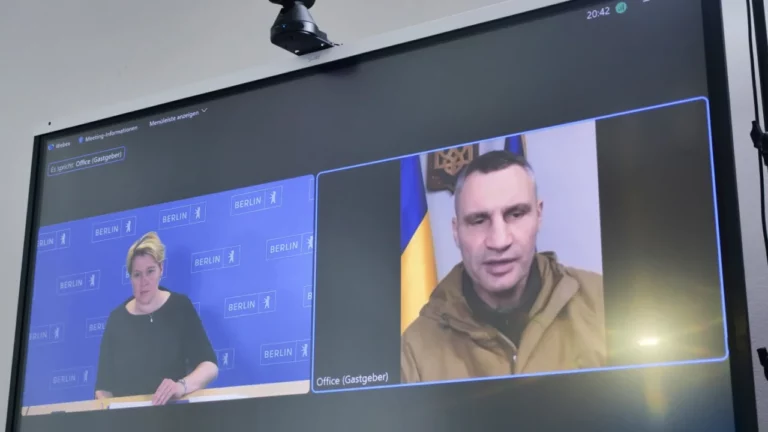
Deep Fakes – Reality vs Manipulation
Ransomware attacks are ubiquitous. Whether through media coverage, stories from the work environment or acquaintances – there is no getting around the topic of cybercrime and especially ransomware. However, the increasing presence has a fact-based origin.
Why ransomware attacks are on the rise

Ransomware attacks are ubiquitous. Whether through media coverage, stories from the work environment or acquaintances – there is no getting around the topic of cybercrime and especially ransomware. However, the increasing presence has a fact-based origin.
Two-factor authentication protects – really?!

Two- or multi-factor authentication is the safety belt of cybersecurity. When used correctly, cyber risks can be reduced, but it does not protect against one’s own negligent behavior. We explain how two-factor authentication works, when it is worth using it and where its limits lie.
Data backup
Data backup This is another term for ‘backup’ and refers to the process of creating backup copies of existing data. For further information, please see the entry for ‘backup’.
Myth or truth: Alexa is always listening!

Voice assistants such as Alexa are there for us on demand. But many users are wondering: Is the voice assistant actually always listening in? And if so, what does that mean?
Cybercriminals infiltrate T-Mobile’s corporate network
26.04.2022 Critical vulnerability in Microsoft Exchange Server Once again, there was a cyber incident at the telecommunications service provider T-Mobile. Criminal hackers have managed to penetrate the company network through stolen credentials and gain access to the operating software. In our blog post, you will learn how the events happened and how companies can protect […]
Scareware
Scareware The term scareware is made up of the English word “scare”, which translates as frightening, and the word part “-ware” of software. Scareware is a program that specifically triggers frightening moments and uses them for fraud attempts. For example, by reporting a fictitious virus discovery and offering a paid program to remove these alleged […]
Rootkit
Rootkit A rootkit is a collection of software tools that cybercriminals can use to gain all the privileges (administrator rights) of a computer or network without being detected. What does that mean in detail? “Root” is the term for the administrator in certain operating systems. In other words, for the user who is equipped with […]

