Multi-factor authentication (MFA)
Multi-factor authentication (MFA) Multi-factor authentication (MFA) is a security procedure that requires users to log in with at least two different factors. In addition to a password, additional proof is required, e.g. a code on the smartphone. What does MFA mean in detail? The MFA combines different types of evidence: Knowledge (e.g. password) Possession (e.g. […]
Free Guide: Better Prompting – How to Use ChatGPT & Co Correctly

We all work with computers on a daily basis. But very few of us know what to do in the event of a cyberattack. Find out with our guide.
Windows 10 is expiring – act now before it’s too late
The Remote Desktop Protocol (RDP) is undoubtedly an invaluable tool for the modern IT infrastructure. It allows users to connect to and control remote computers over the network. This function is particularly popular in companies for IT administration, whether for support or remote maintenance of systems.
In Focus: Artificial Intelligence as an Attack Vector, Example: Deepfakes
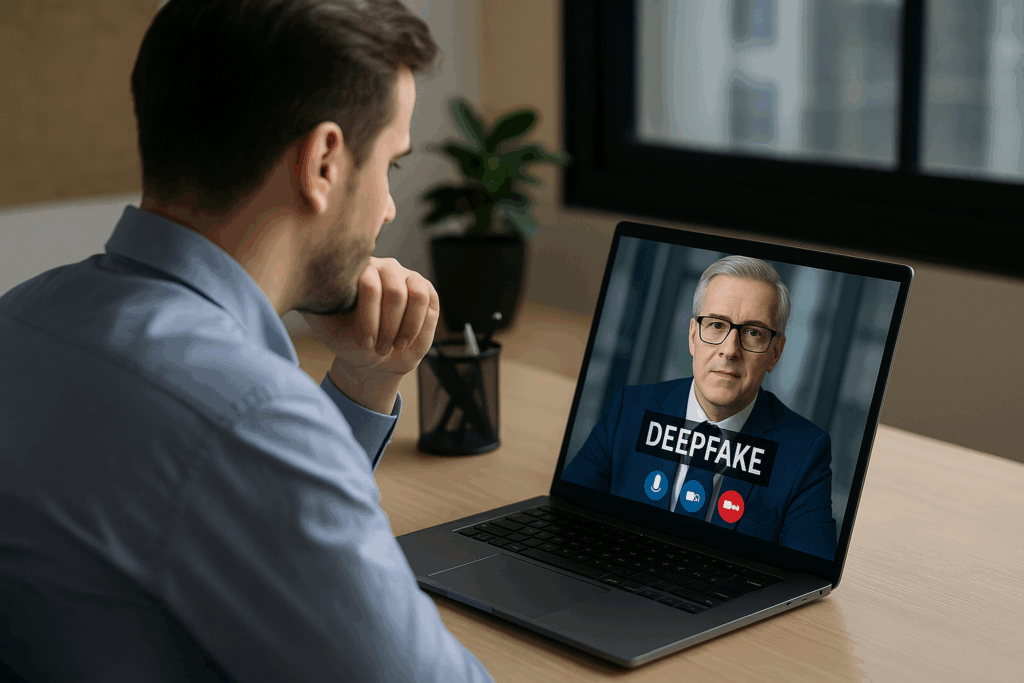
Artificial intelligence opens up new, fascinating possibilities – unfortunately also for cybercriminals. They are increasingly using so-called deepfakes: AI-generated fakes of videos, images or voices that are used in the work environment for deceptively real attacks.
In Focus: Business Email Compromise

Business email compromise is a targeted form of digital fraud in which attackers exploit internal business processes through manipulated or compromised email communication. The goal is to redirect payments, steal sensitive data or manipulate processes.
Critical vulnerability in Microsoft SharePoint
There is a critical vulnerability in Microsoft Windows (CVSS 9.8) that affects almost all current Windows and server versions and allows attackers to execute malicious code with system privileges without user interaction – an acute risk to your IT infrastructure
Critical vulnerability in Windows authentication
There is a critical vulnerability in Microsoft Windows (CVSS 9.8) that affects almost all current Windows and server versions and allows attackers to execute malicious code with system privileges without user interaction – an acute risk to your IT infrastructure
Critical vulnerabilities in Citrix NetScaler
Several critical vulnerabilities in Citrix NetScaler ADC and Gateway allow attackers to take over active web sessions, sometimes even bypassing multi-factor authentication.
New Phishing Wave: Dangerous Scripts in SVG File Attachments
Currently, security organizations and the Austrian CERT are registering an increase in targeted phishing attacks, in which malicious code is injected via seemingly harmless vector graphics.
In focus: Car dealerships are easy victims of e-mail fraud

Companies in various industries nowadays rely heavily on email communication and online transactions for their business operations. However, as efficient as this way of doing business is, it also opens the door to cybersecurity threats, such as email and wire fraud.

