
The word “quishing” is a combination of the term “phishing” and the abbreviation “QR” and describes phishing attacks via a QR code.
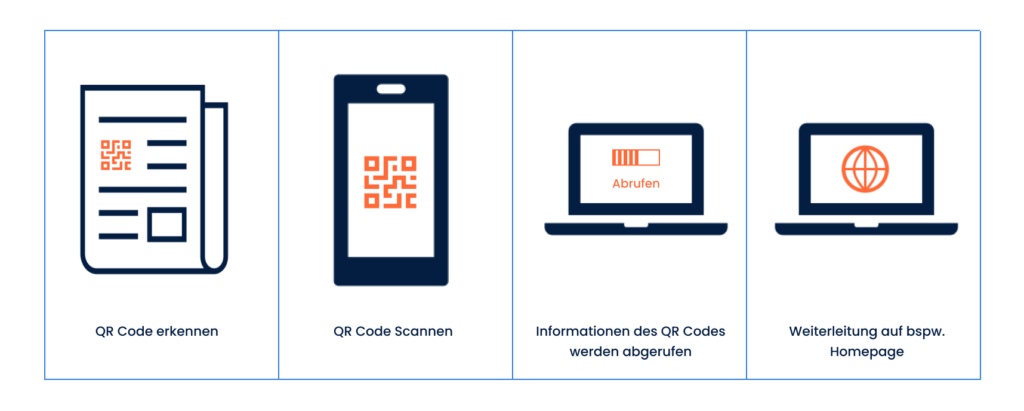
Excursus: What is a QR code? QR stands for “Quick Response”. It is a two-dimensional code that displays information in a highly abbreviated form and can be called up by scanning the QR code. The codes can be read with the camera of a smartphone. Barcodes in supermarkets work in a similar way. However, the QR code can process more information. The user can be directed to homepages, images, videos, text files, etc.
The criminals’ motivation for quishing is no different from any other Phishing methods. Here too, the focus is on tempting users to take quick, ill-considered action. In this way, the attackers want to obtain confidential and personal information and/or install malware on the target’s systems. As with conventional phishing, triggers are used: Urgency is suggested, the user is asked to exercise caution or curiosity is aroused by offering exclusive knowledge or special offers.
For example, you can receive emails with QR codes for new offers, certain additional services or bargains that are only valid for you and only for a short time.
Or you will receive a message asking you to update your access data. Using the QR code, you will be redirected quickly and easily to the website of the supposed provider. You may also be asked to download documents or certain files.
If the victims fall for the quishing attempt and follow the request to scan the QR code, they may immediately download malware or enter sensitive data on a fake website, which then also falls into the hands of the cybercriminals. The attackers can then use the information for their criminal purposes, for example by gaining access to computers, networks and systems or sending malware to captured contact files.
Personal information, customer data, user data, access data and also payment data are of particular interest to threat actors. Criminal hackers use QR codes to direct users to fraudulent websites. If the user name and password are entered there, these are also known to the cybercriminals. If the victims also enter payment information, this information also falls into the hands of the cybercriminals.
In principle, everywhere. The use and acceptance of QR codes is increasing massively. As they can be used easily, quickly and contactlessly, more and more companies are opting to use QR codes. The method is also becoming increasingly popular with users. More and more people know how to use them and scan the codes to call up offers, contact details, information, current notices, timetables and the like. Criminal hackers are taking advantage of this. Even if conventional phishing e-mails or Smishing (phishing via SMS) is still widespread at present, quishing represents a growing threat.
The BSI(German Federal Office for Information Security) is currently warning against this type of attack because, on the one hand, the URL behind QR codes is difficult for employees to recognize. On the other hand Spam filters already filter out a large number of phishing emails, but QR codes still pose challenges for the filters. IT security solutions scan attachments and URLs to filter out phishing emails. However, a QR code is often perceived as a harmless image file and thus overcomes the protective measures.
At the moment, people are being “harvested” in the name of Microsoft – specifically the Microsoft 365 cloud service. The first step is to tap into user data. In the second step, the affected users are then redirected to a fake login page for Microsoft 365, which looks amazingly real. Access data is then intercepted here and used for further cyber attacks.
![]() Our tip:
Our tip:
Smartphones are part of everyday working life for many people. Whether you have a company smartphone or use your personal smartphone for work, the security standards for mobile devices must be defined and made accessible to all employees. The purposes for which the smartphone may be used must be clearly regulated. In addition, the smartphone must comply with current security standards. Important security updates must always be carried out promptly and 2-factor or multi-factor authentication should be used if this is sensible and possible.