Due to a security vulnerability in Microsoft Exchange servers, tens of thousands of email servers of companies, authorities and educational institutions have fallen victim to hacker attacks, according to US media reports. Four of the recently disclosed Microsoft vulnerabilities have been exploited by hackers. There could be more than 250,000 victims worldwide, according to the Wall Street Journal.
On Sunday, the European Banking Authority (EBA) also announced that unauthorized persons may have had access to e-mails. There are also likely to be thousands of victims in Germany. According to the German Federal Office for Information Security (BSI), six federal agencies are also affected by the hacker attacks on Microsoft e-mail programs. In four cases, there was a possible compromise. It is still true that the security updates provided by Microsoft should be installed as soon as possible.
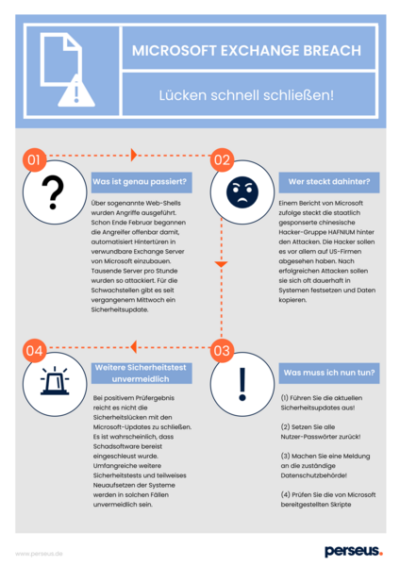
What happened?
The first indications of these vulnerabilities had already been given on February 28 by the IT security company Volexity from the US state of Virginia. Analysts had found several attacks that had been carried out via so-called web shells, i.e. input tools for system commands. As early as the end of February, the attackers apparently began to automatically install backdoors in vulnerable Microsoft Exchange servers. Thousands of servers per hour were attacked in this way. There has been a security update for the vulnerabilities since last Wednesday. However, experience has shown that it takes quite a while for updates from all affected companies to be installed.
Who is behind it?
According to a report by Microsoft, the state-sponsored Chinese hacker group HAFNIUM is behind the attacks. The hackers are said to have targeted US companies in particular, for example from the industrial sector, educational institutions and NGOs. After successful attacks, they are often said to become permanently entrenched in systems and copy data.
What do I have to do now?
Run the latest security updates!
The developers have published secured editions for the following vulnerable Exchange server versions:
To enable admins to quickly check their installed Exchange Server versions,
Microsoft provides a script for download . With the security updates, the developers are closing three more vulnerabilities (CVE-2021-26412, CVE-2021-26858, CVE-2021-27078), but no attackers are said to be targeting them at the moment.
According to Microsoft, Exchange Online is not affected by the vulnerabilities.
>> Reset all user passwords!
>> Make a report to the responsible data protection authority!
This way you can be sure that you do not miss the applicable deadlines.
>> Review the scripts provided by Microsoft and use other analysis tools to see if your organization has been compromised. However, companies that have not secured their Exchange servers can in principle assume that they will be affected.
Further security tests inevitable
As part of its commitment to more IT security in SMEs, the BSI today sent a letter directly to the management of those companies whose Exchange servers are affected to the BSI’s knowledge, makingrecommendations for countermeasures .
According to security experts, if the test result is positive, it will not always be sufficient to close the security gaps with Microsoft updates. Rather, it is to be expected that in such cases further malware has already been infiltrated. Extensive further security tests and partial reinstallation of the systems will be unavoidable in such cases.
The experts at Perseus strongly recommend keeping the software up to date. In addition, it is recommended to conduct checks on the available IOCs related to the vulnerabilities associated with this incident. The list is available here .
Feel free to contact us if you want to know how you can further improve your company’s cyber security in the long term!