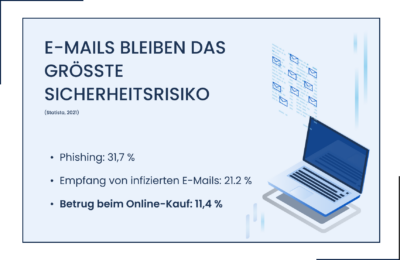
Companies in various industries nowadays rely heavily on email communication and online transactions for their business operations. However, as efficient as this way of doing business is, it also opens the door to cybersecurity threats, such as email and wire fraud.

The Perseus Incident Response Management Team is observing an increase in email fraud cases in the automotive industry. Employees of car dealers were affected. Believing that they were in contact with reputable companies that offered dealers the prospect of buying vehicles cheaply for resale, those affected corresponded with malicious actors instead of legitimate sellers and fell victim to attempts at deception with great financial losses.
This article analyzes the sophisticated nature of these scams and draws conclusions on securing businesses that are relevant across industries and affect all businesses equally.
 It all started seemingly harmlessly: employees of car dealers received routine emails from a well-known car rental company that offered cars for sale to car dealers at low prices – in some cases even at generous discounts. This is a common practice in the automotive industry. The employees trusted the legality of the e-mails, corresponded with the senders and finally received definitive offers to buy the vehicles.
It all started seemingly harmlessly: employees of car dealers received routine emails from a well-known car rental company that offered cars for sale to car dealers at low prices – in some cases even at generous discounts. This is a common practice in the automotive industry. The employees trusted the legality of the e-mails, corresponded with the senders and finally received definitive offers to buy the vehicles.
In the further course of the correspondence, everything went according to the usual business processes. Employees received authentic-looking emails and documents, including invoices in the design of the car rental. All the information in the emails matched the original data of the car rental company, except for a slightly modified domain.
Believing in the authenticity of the communication, the employees carried out the transactions and paid large amounts for the vehicles as instructed. Over time, however, doubts arose among the employees. Despite payments made, they did not receive registration certificates for the vehicles, which are usually handed out immediately after purchase. Worried, they contacted the supposed seller, the car rental company, only to find that there were no records of the transaction. The car dealerships had fallen for a scam.
Upon closer inspection, it turned out that the communication came from an attacker who had set up a deceptive domain and email address that mimicked that of the legitimate company. What initially looked like a legitimate business transaction turned out to be a sophisticated case of email and wire fraud. It was pretended to sell vehicles from the car rental company’s stock at a significantly lower price. Particularly treacherous: The vehicles promised by the criminals were actually listed for sale online by the car rental company.
In this case, however, the target persons only communicated with third parties via a third-party domain that was created for the fraud. The attackers carefully crafted emails and documents and mimicked the car rental company’s style and branding, making it nearly impossible for employees to recognize the fraudulent nature of the communication.
The threat actors also forged convincing invoices with bank details for payment. Only through the bank details could it have been noticed that the account holder was a third party. Here, too, the fraudsters could have given a different name, as banks have only checked the IBAN for years.
The attackers took advantage of the common business practice of buying vehicles via email and abused the familiarity of the process to successfully carry out their fraud attempt.
The forensic investigation by Perseus’ Incident Response Team revealed that the incident was a type of email and wire transfer scam that is currently targeting various car dealerships. Some of the emails in question were not specifically addressed to the companies, but to several recipients at the same time. This is known as “undisclosed recipients”. This method is used to disguise the actual recipients of the email.
After a thorough examination of the received invoice document, the forensic analysis did not reveal any further information about the identity of the perpetrator. The invoice was labeled “Microsoft Word for M365”. This seems atypical for this process.
Further investigations revealed that the Internet domain registered by the attacker had also been deleted at the time of the check – presumably at the instigation of the company or the domain provider. The Perseus team of experts was unable to access the registrant’s data due to GDPR regulations.
The incident highlights the vulnerability of businesses to email and wire fraud and highlights the need for increased security measures and closer scrutiny of email communications. The Perseus team of experts recommended that the affected car dealerships file criminal charges in order to be able to take further legal action against the perpetrator. A suitable point of contact is the “Central Contact Point for Computer Crime”. It is a specialized agency that has experience in dealing with cybercrime cases.
 In addition, the client was advised to specifically raise awareness of cyber threats among its employees, specifically how to identify and mitigate the risks associated with email and financial fraud.
In addition, the client was advised to specifically raise awareness of cyber threats among its employees, specifically how to identify and mitigate the risks associated with email and financial fraud.
The policyholder was also strongly advised to revise the purchase process and the business transaction. Further verification steps, such as telephone confirmation directly with the seller’s parent company, should be set up to confirm the legitimacy of transactions and prevent similar incidents in the future. In particular, the IBAN should be cross-checked in order to easily uncover fraud.
By taking active measures such as reporting the incident, investing in employee training, and streamlining the buying process, companies can strengthen their protection against email and wire fraud.
The present scenario is by no means limited to the automotive industry. Similar tactics could be used in different industries with similar buying processes. Industries such as real estate, manufacturing, and wholesale often process transactions via email or bank transfer. The fraudulent techniques used in this case serve as a cautionary tale for companies in all industries that are vulnerable to fraudulent activity.