
In recent days, information has been accumulating that there is an increase in malware attacks on German companies. Furthermore, a research team from the security software manufacturer Kaspersky discovered a dangerous boot kit. This new type of malware still raises questions. We get to the heart of what it is, who is at risk and how you can protect yourself.
German companies increasingly attacked with malware “Hyberbro”
In its Cyberbrief 01/22, the Federal Office for the Protection of the Constitution warns of an ongoing espionage campaign by the APT 27 group.
According to the Office for the Protection of the Constitution, the attackers use a Remote Access Trojan (RAT) called “Hyberbro”. A RAT is a malware program that opens a backdoor for administrative control on the targeted system. RATs are usually downloaded in the background by a program that has been called by the user. In the current case, it is suspected that the malware was installed on countless computers by exploiting security vulnerabilities in the password management program AdSelfService Plus1 from the Indian software manufacturer Zoho. The vulnerability in Microsoft Exchange, which became known in March, is also considered an entry gate for “Hyberbro”, as many companies have still not closed the gap.
This type of cyberattack focuses primarily on the theft of trade secrets and intellectual property. However, the Office for the Protection of the Constitution does not rule out the possibility that the attackers could also penetrate the networks of customers and service providers via this route and infiltrate several companies at once.
For experts: Possible indicators of infection
Cyberbrief 01/22 also contains information on how to detect an infection with “Hyberbro”. Among the indications that indicate a compromise of a system (Indicators of Compromise, IOC) are three IP addresses to which the RAT seeks contact:
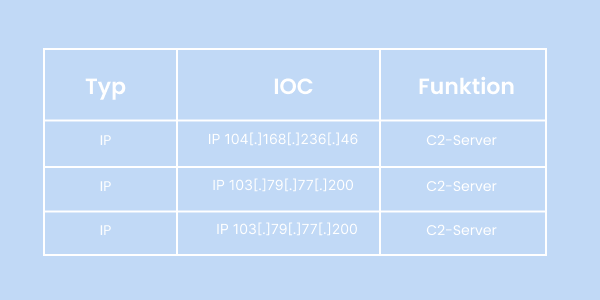
Furthermore, certain files, paths or processes can also indicate an infestation. All details can be found in the Cyberbrief 01/22 of the Federal Office for the Protection of the Constitution.
What you can do
We advise admins and IT managers:
Security professionals identify new “MoonBounce” bootkit
Furthermore, security researchers from Kaspersky have found a new, dangerous bootkit called “MoonBounce” on a customer’s computer. A bootkit is a malware program that nestles in the motherboard and spreads via the Unified Extensible Firmware Interface (UEFI). The UEFI serves as an interface and contains information that is used on the computer to load the operating system. This means that malicious code contained in it is executed even before the operating system boots up.
This allows MoonBounce to bypass most security mechanisms and control operating system boots undetected, as well as modify system code and drivers before anti-virus and other security components are loaded.
If a computer is infected, either the SPI error memory must be reloaded or the entire motherboard must be replaced.
It is currently unclear how the device was infected with “MoonBounce”. However, it is believed that this was done remotely. Since the development of a boot kit like MoonBounce is a rather complex matter for which traditional cybercriminals have hardly any resources at their disposal, it is assumed that the goals are mainly economic and state-level. Due to the nature of the malware, Kaspersky experts suspect a team called ATP41 as part of “MoonBounce”, which is believed to come from China.
What you can do