Sooner or later, every computer user is confronted with the terms authorization and authentication. Very often the question arises in your daily life: Do I have access to this file? Am I allowed to share this folder with my colleague? And what was 2-factor authentication again? Read here where you may encounter the different forms and how they differ from each other.
You already encounter authorization and authentication more often than you may realize. It is enough to describe a normal working day in the office.
Authentication is omnipresent
It’s 7:30 a.m. You’re on the train on your way to the office, and you want to check your email on your smartphone from there. To unlock the phone, you either enter a pin, use your fingerprint or the built-in facial recognition – all examples of authentication. Next, you open the email program on your phone and may need to enter a password. Again, you must confirm your identity to the program through some type of authentication. Once in the office, you sit at your desk and log on to your computer. Again, you identify yourself through authentication (e.g., a password).
In these three cases, after you have authenticated yourself, the system checks whether the user name matches the password you entered and whether the combination exists. This means that your entries are now authenticated. If they are correct and can be assigned to a specific identity, you can now access and use the device, application or program with the access rights of precisely this identity.
2-factor authentication offers special protection
Before the next meeting, you need to make a bank transfer. To do this, you log in to the online banking of the financial institution where you have the account. Here, too, you are asked for a password – an authentication – which is also subsequently authenticated. But now the banking institution asks for additional confirmation of your identity. This can be in the form of security questions that you have to answer. Or you may be sent a pin or code to a second device, such as your smartphone. Only after entering this information will you gain access to the system and be able to make the transfer. This is called 2-factor authentication. Unlike authentication, which is usually activated by default in the system, you have to activate 2-factor authentication yourself. But once enabled, it provides extra protection for you and your data.
Authorizations grant entry and access
After lunch, your supervisor calls you in for a meeting. This takes place in a conference room that is normally reserved for the management team. To enter the room, the door must be opened for you or your access card, which you normally use to move around the office building, must be unlocked for this area – before that, you are not authorized.
Your boss asks you to revise a colleague’s document for a meeting that is due in an hour. When you open the file, you are then told that you do not have access to it. Since your colleague works in a different department, you lack the appropriate authorization. You have to ask the colleague if you are allowed to edit this file. The colleague answers promptly and gives you permission. Now you are authorized to read and edit this file.
Perseus’ tip: For security reasons, it is quite advisable to customize folder accesses. Certain files do not need to be publicly available to the entire workforce, they should only be made accessible to a specific group of people. Data breakdowns and data loss can be limited in this way.
Authorization for program installations
By now it’s 17:30, and your workday is coming to an end. Before you can leave, however, your computer indicates that an important update needs to be installed. Since updates are supposed to be installed immediately, you click the notification to start the installation. However, the system requires an account with admin rights for this, which you do not have with your account. You therefore lack the appropriate authorization to carry out the process. You must obtain this from the person responsible. In most cases, the company’s IT admin will connect to your computer and authorize the installation of the update through their own account or give their account (temporarily, if necessary) the appropriate extended rights.
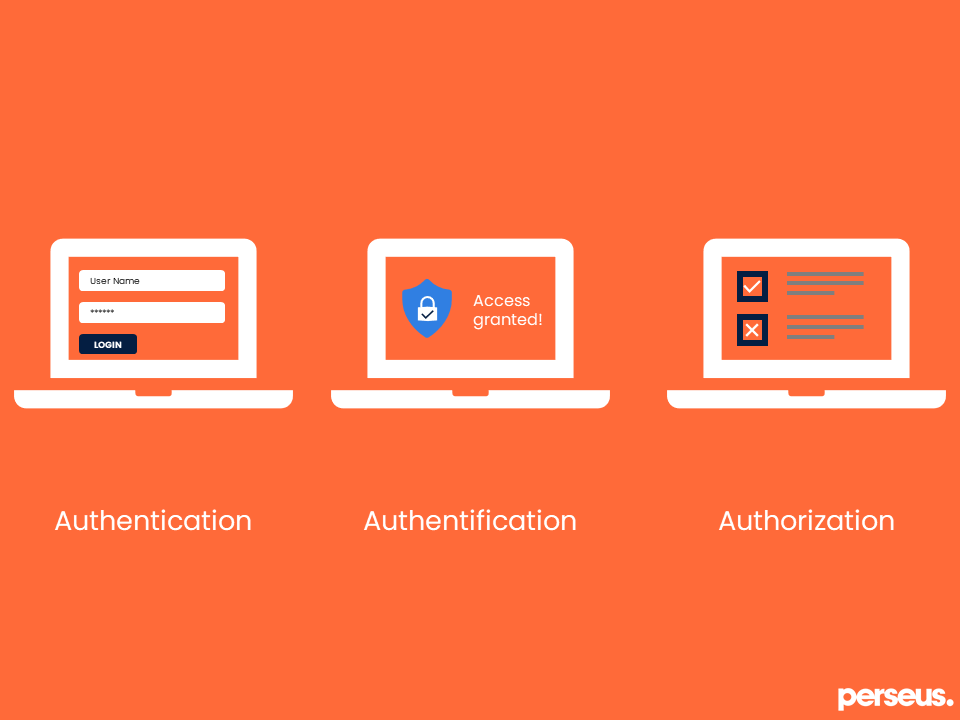
With this sentence, you can easily remember the differences between the terms:
First level of authentication is the specification of an identity, the second level of authentication is the confirmation of an identity, and authorization is the authorization of an identity.